In the world of cryptocurrency, securing transactions without a central authority is one of the biggest challenges. Proof of Work (PoW) is a consensus mechanism that plays a crucial role in ensuring the integrity and security of blockchain networks. Originally introduced with Bitcoin, PoW allows decentralized participants, known as miners, to validate transactions by solving complex mathematical puzzles. This process not only prevents fraudulent activities like double-spending but also strengthens the overall security of the network by making it computationally expensive to alter past records. While PoW is widely recognized for its reliability and resistance to attacks, it also faces criticism for its high energy consumption and scalability limitations. In this article, we’ll explore how PoW works, its role in validating transactions, and the advantages and drawbacks of this widely used consensus mechanism.
What is Proof of Work (PoW)?
Proof of Work (PoW) is a consensus mechanism used in blockchain networks to verify transactions and maintain the security of the system without relying on a central authority. It requires network participants, known as miners, to solve complex mathematical puzzles to validate new transactions and add them to the blockchain. This process ensures that only legitimate transactions are recorded while making it extremely difficult for malicious actors to alter the network’s history. The concept of PoW was first introduced in Bitcoin’s whitepaper by Satoshi Nakamoto and has since been adopted by several other cryptocurrencies, including Litecoin and Dogecoin. PoW enhances network security by making attacks computationally expensive and economically unfeasible. However, its high energy consumption and slower transaction speeds have sparked debates about its long-term sustainability compared to alternative consensus mechanisms like Proof of Stake (PoS).
 How Proof of Work (PoW) Works
How Proof of Work (PoW) Works
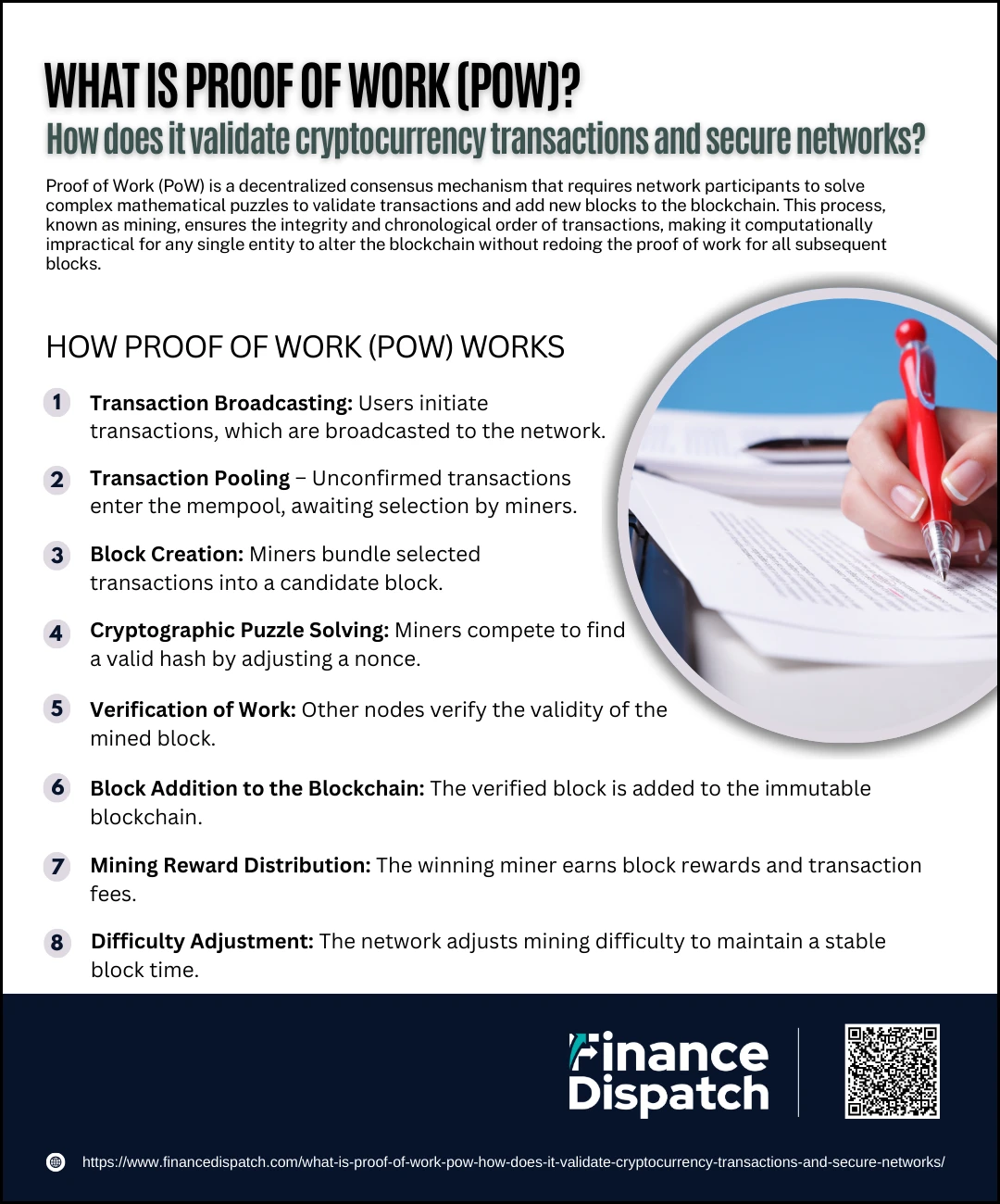
Proof of Work (PoW) is a mechanism that ensures security, transparency, and decentralization in blockchain networks. It operates by requiring miners to compete in solving cryptographic puzzles, which demand substantial computational power. The first miner to solve the puzzle earns the right to add a new block of verified transactions to the blockchain. This process not only validates transactions but also secures the network by making it extremely difficult to alter past records. Below is a detailed step-by-step breakdown of how PoW works:
Step-by-Step Process of Proof of Work (PoW)
1. Transaction Broadcasting – Users initiate cryptocurrency transactions, which are then broadcasted to the network. These transactions remain unconfirmed until they are included in a mined block.
2. Transaction Pooling – Unconfirmed transactions enter a waiting area known as the mempool, where miners select which transactions to include in the next block. Priority is often given to transactions with higher fees.
3. Block Creation – A miner bundles selected transactions into a candidate block. Each block includes transaction details, a reference to the previous block, and a random number called a nonce.
4. Cryptographic Puzzle Solving – Miners compete to find a valid hash by modifying the nonce until the hash meets the network’s difficulty requirements. This process requires substantial computational power and energy.
5. Verification of Work – Once a miner discovers a valid hash, they broadcast their solution to the network. Other miners and nodes verify the solution to ensure that it meets the difficulty target and adheres to network rules.
6. Block Addition to the Blockchain – If the block is verified as valid, it is added to the blockchain, making all included transactions immutable. This ensures that transaction history remains secure and unchangeable.
7. Mining Reward Distribution – The winning miner receives a reward in newly minted cryptocurrency along with transaction fees collected from the included transactions. This incentivizes miners to continue securing the network.
8. Difficulty Adjustment – To maintain a consistent block creation time (e.g., every 10 minutes in Bitcoin), the network adjusts the mining difficulty periodically. If blocks are mined too quickly, the difficulty increases; if they are mined too slowly, it decreases.
 How PoW Validates Cryptocurrency Transactions
How PoW Validates Cryptocurrency Transactions
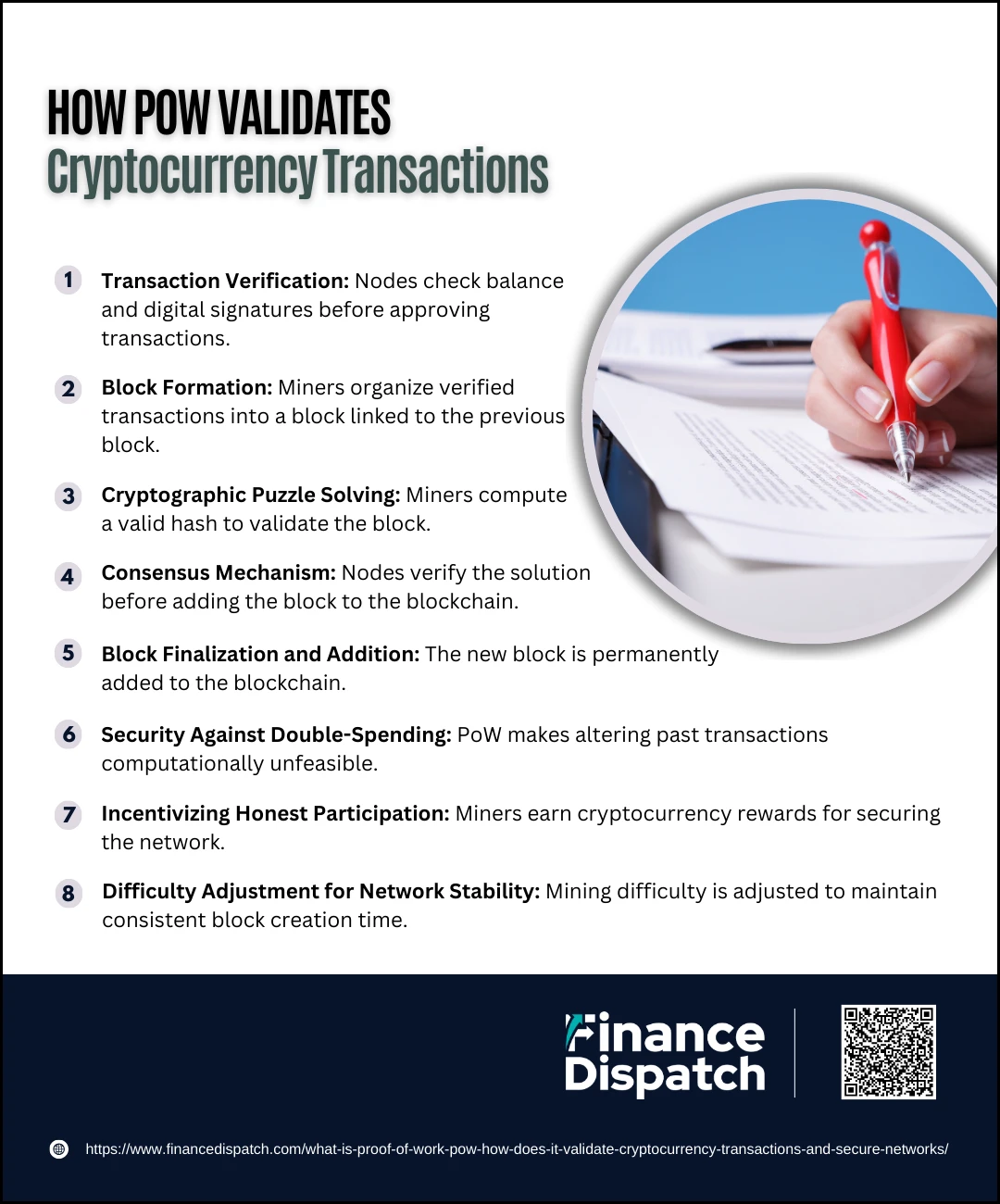
Proof of Work (PoW) plays a crucial role in ensuring the security and legitimacy of cryptocurrency transactions. In a decentralized blockchain network, there is no central authority to verify or approve transactions, making it necessary to have a mechanism that prevents fraud, double-spending, and network manipulation. PoW achieves this by requiring miners to perform complex mathematical computations before adding transactions to the blockchain. This computational process ensures that only valid transactions are recorded and that altering previous records becomes nearly impossible due to the high energy and cost required. Below is a detailed look at how PoW validates cryptocurrency transactions.
1. Transaction Verification
Before a transaction can be added to the blockchain, the network nodes validate it. They check if the sender has enough balance to complete the transaction and ensure that the digital signature matches the sender’s private key. If the transaction is valid, it is added to a pool of pending transactions known as the mempool. Invalid transactions are rejected automatically.
2. Block Formation
Miners collect verified transactions from the mempool and organize them into a candidate block. Each block contains multiple transactions, a timestamp, a reference to the previous block (hash of the last block), and a random number called a nonce. The reference to the previous block ensures that all blocks are linked, forming a secure and continuous chain.
3. Cryptographic Puzzle Solving
To validate the transactions within a block, miners must solve a cryptographic puzzle by finding a valid hash. This process involves continuously changing the nonce and re-hashing the block’s data until a hash is produced that meets the network’s difficulty target. Since this process requires significant computational resources, it makes fraudulent activities extremely costly and impractical.
4. Consensus Mechanism
Once a miner finds the correct hash, they broadcast the solution to the entire network. Other nodes independently verify the solution to ensure that it meets the required difficulty level and follows network rules. This step prevents dishonest miners from adding false or manipulated transactions to the blockchain.
5. Block Finalization and Addition
After the solution is confirmed as valid, the new block is permanently added to the blockchain. Every node in the network updates its copy of the blockchain to reflect the newly added block, ensuring consistency across the entire network. Transactions within that block are now considered final and immutable.
6. Security Against Double-Spending
One of the main threats in cryptocurrency transactions is double-spending, where a user attempts to spend the same digital coin more than once. PoW prevents this by ensuring that once a transaction is added to the blockchain, it cannot be reversed or altered without an enormous amount of computational power. To modify an old transaction, a malicious actor would need to re-mine that block and all subsequent blocks, which becomes exponentially difficult as more blocks are added.
7. Incentivizing Honest Participation
To encourage miners to participate honestly and secure the network, they receive rewards in the form of newly minted cryptocurrency (block rewards) and transaction fees. This economic incentive ensures that miners remain committed to verifying transactions and maintaining network integrity.
8. Difficulty Adjustment for Network Stability
To maintain a consistent rate of block creation (e.g., one block every 10 minutes in Bitcoin), the network periodically adjusts the mining difficulty. If blocks are being mined too quickly, the difficulty increases, making it harder to find a valid hash. If blocks are being mined too slowly, the difficulty decreases, making it easier to find a valid solution. This adjustment keeps the network stable and prevents sudden disruptions.
 How PoW Secures the Blockchain Networks
How PoW Secures the Blockchain Networks
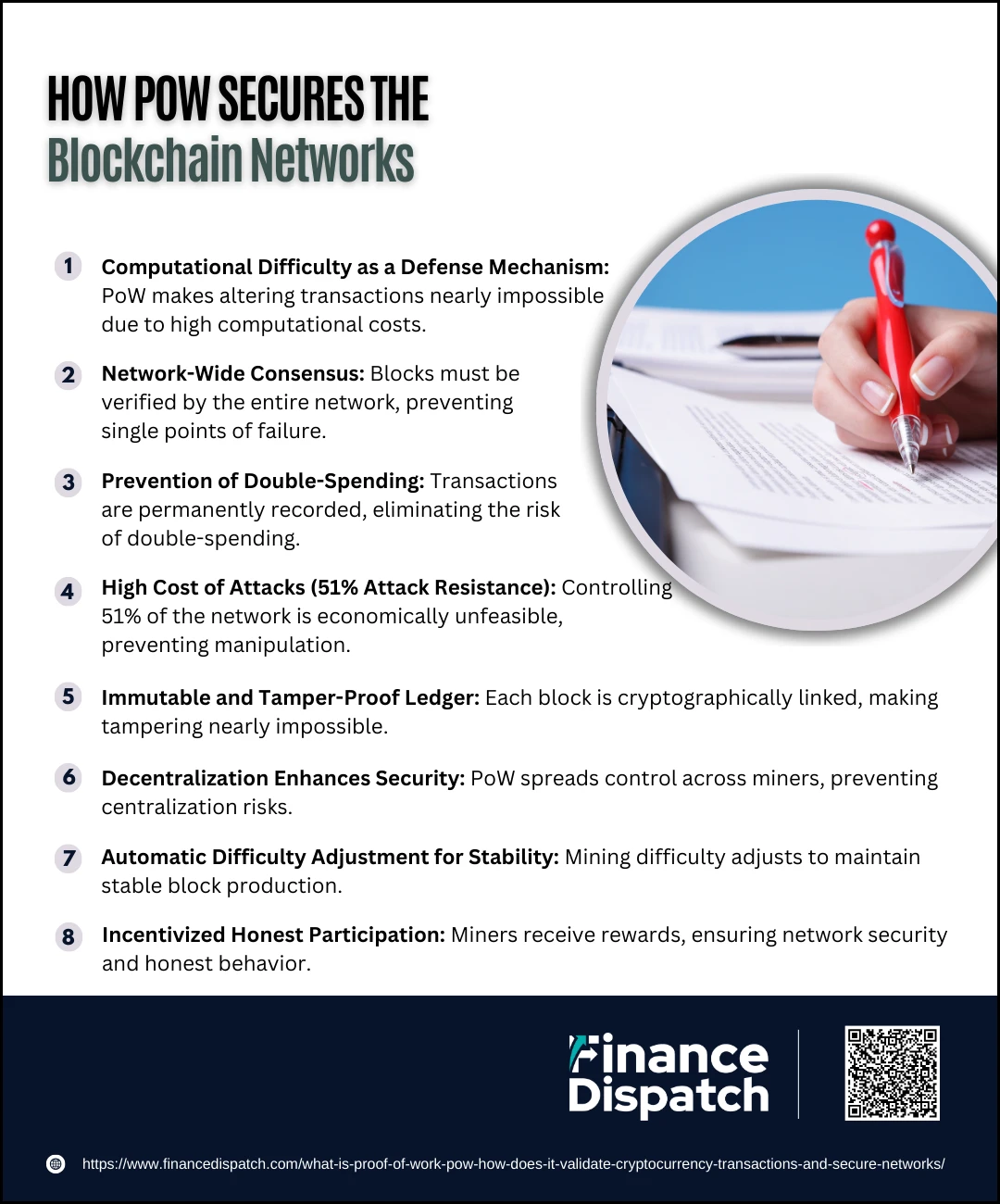
Proof of Work (PoW) is a fundamental mechanism that ensures the security and integrity of blockchain networks. By requiring miners to solve complex mathematical puzzles, PoW makes it computationally expensive and time-consuming for malicious actors to alter the blockchain. This mechanism not only prevents fraud, such as double-spending, but also strengthens network decentralization by allowing multiple participants to validate transactions. Below are the key ways PoW secures blockchain networks:
1. Computational Difficulty as a Defense Mechanism
PoW requires miners to perform extensive computations to find a valid hash. This process makes it nearly impossible for an attacker to alter previous transactions since they would need to redo the work for all subsequent blocks.
2. Network-Wide Consensus
Each new block must be verified by the entire network before being accepted. This decentralized verification process prevents single points of failure and ensures that no entity can unilaterally modify blockchain data.
3. Prevention of Double-Spending
Since PoW mandates that transactions be included in a block and confirmed across the network, it eliminates the possibility of double-spending. Once a transaction is recorded on the blockchain, it is immutable and cannot be reversed.
4. High Cost of Attacks (51% Attack Resistance)
For an attacker to manipulate the blockchain, they would need to control more than 51% of the total network’s computational power. Given the enormous energy and hardware costs involved, this attack is impractical and economically unfeasible for large PoW networks like Bitcoin.
5. Immutable and Tamper-Proof Ledger
PoW ensures that every block is cryptographically linked to the previous one, forming a chain of blocks (blockchain). Any attempt to modify a past transaction would require re-mining all subsequent blocks, making tampering virtually impossible.
6. Decentralization Enhances Security
Unlike centralized systems that can be hacked or manipulated, PoW spreads control across thousands of independent miners worldwide. This decentralization prevents any single entity from taking over the network and ensures trustless security.
7. Automatic Difficulty Adjustment for Stability
The PoW mechanism continuously adjusts mining difficulty to maintain a steady block production rate. This prevents rapid mining that could compromise security or cause network instability.
8. Incentivized Honest Participation
Miners are rewarded with cryptocurrency for securing the network. This economic incentive ensures that miners act honestly, as any attempt to cheat the system would result in financial loss and wasted energy.
 Advantages of Proof of Work
Advantages of Proof of Work
Proof of Work (PoW) is a consensus mechanism that has played a crucial role in the security and decentralization of blockchain networks. By requiring miners to solve complex mathematical puzzles to validate transactions and add new blocks, PoW ensures that no single entity can manipulate the blockchain. While it has faced criticism for its energy consumption, PoW continues to be one of the most secure and time-tested methods for achieving decentralized consensus. Below are some of the key advantages of PoW:
1. High Level of Security
PoW offers one of the most secure methods for validating transactions in a blockchain network. The computational effort required to solve cryptographic puzzles makes it incredibly difficult for hackers to alter transaction records. Any attempt to manipulate the blockchain would require immense computational power, making attacks highly impractical and costly.
2. Decentralization and Censorship Resistance
One of the core principles of blockchain technology is decentralization, and PoW effectively achieves this by distributing mining power across a vast network of independent participants. Unlike traditional financial systems where a central authority controls transactions, PoW networks allow anyone with computing power to participate, making the system resistant to censorship and government interference.
3. Protection Against Double-Spending
A major concern in digital currencies is the risk of double-spending, where a user tries to spend the same cryptocurrency multiple times. PoW prevents this by requiring miners to validate transactions and ensure that each digital coin is only used once. Once a transaction is recorded in a block and added to the blockchain, it becomes nearly impossible to alter.
4. Proven Track Record
PoW has been successfully securing blockchain networks for over a decade, particularly with Bitcoin, the first and most valuable cryptocurrency. Despite numerous attempts to attack or manipulate Bitcoin, its PoW mechanism has remained highly resilient, proving its reliability as a consensus mechanism.
5. Immutable and Tamper-Proof Ledger
Once a block is added to the blockchain, it is permanently recorded and cannot be modified. Since each block is cryptographically linked to the previous one, altering a single block would require re-mining all subsequent blocks. This makes PoW networks tamper-proof and highly resistant to data manipulation.
6. Open Participation and Equal Opportunity
PoW allows anyone with sufficient computational resources to participate in the mining process. Unlike Proof of Stake (PoS), which favors those with more cryptocurrency holdings, PoW ensures that network security is maintained through work rather than wealth, promoting fairer competition among participants.
7. Economic Incentives for Miners
To encourage miners to secure the network, PoW offers rewards in the form of newly minted cryptocurrency and transaction fees. This economic incentive ensures continuous participation, reinforcing the network’s stability and security. Miners invest in powerful hardware and electricity, making it in their best interest to act honestly and maintain network integrity.
8. Automatic Difficulty Adjustment for Stability
PoW networks like Bitcoin adjust mining difficulty based on the overall computational power in the network. If mining becomes too fast, the difficulty increases; if it becomes too slow, the difficulty decreases. This self-regulating mechanism ensures that blocks are added at a consistent rate, maintaining the stability of the blockchain.
9. Fair Competition Among Miners
Unlike Proof of Stake, where validators are chosen based on the amount of cryptocurrency they hold, PoW rewards miners based on computational effort. This means that success in mining is determined by actual work rather than ownership, fostering a more competitive and fair environment.
10. Resistance to Sybil Attacks
A Sybil attack occurs when a single entity creates multiple fake identities to gain control over a network. PoW prevents this by making mining dependent on computational work, which requires significant resources. Since attackers would need massive amounts of energy and hardware to manipulate the network, Sybil attacks become nearly impossible in PoW-based blockchains.
11. Energy Usage as a Security Feature
While PoW is often criticized for its high energy consumption, this aspect actually strengthens its security. The energy-intensive nature of PoW acts as a barrier against malicious actors, as attempting to alter blockchain records would require an impractical amount of resources. This ensures that transactions remain secure and immutable.
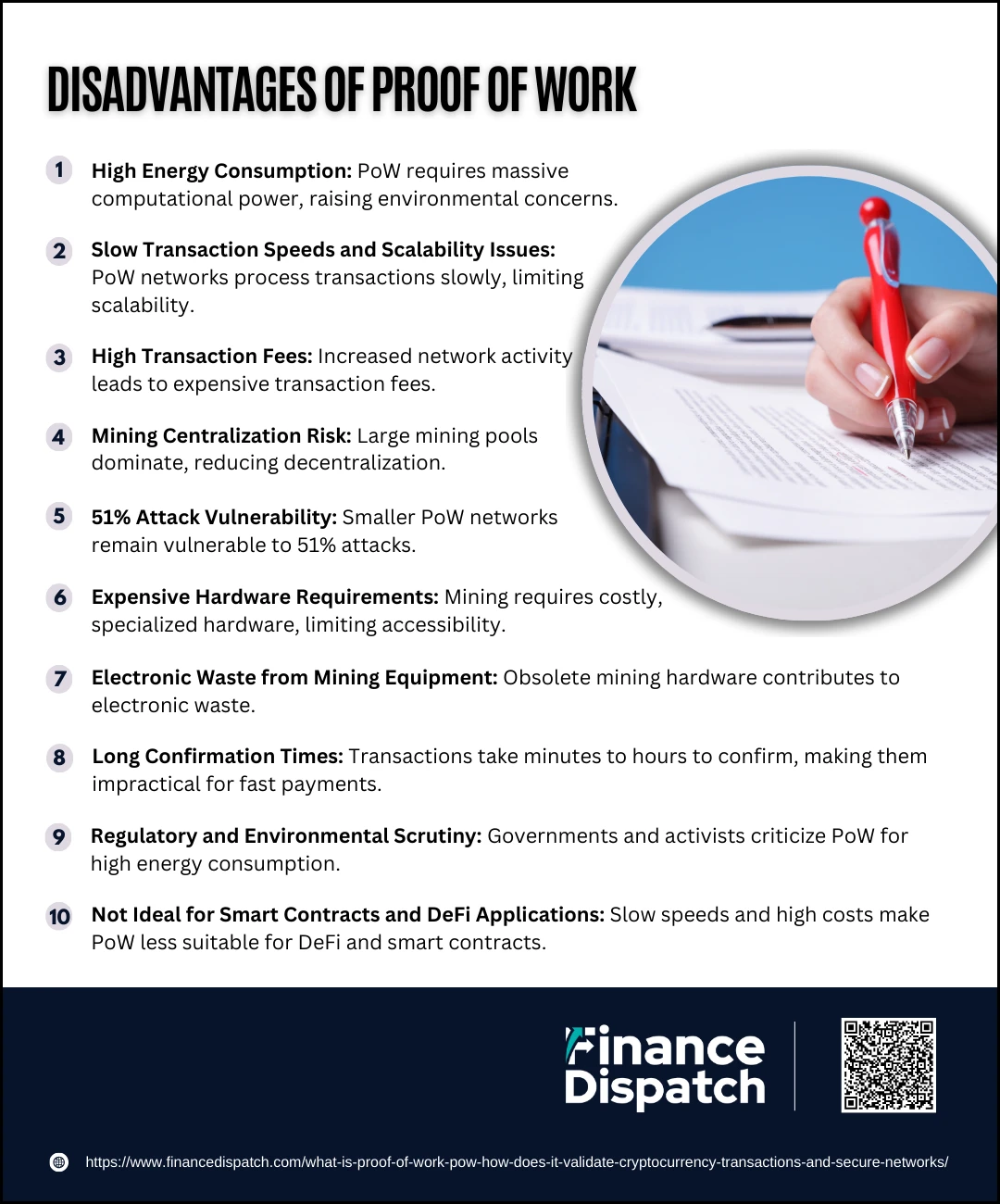 Disadvantages of Proof of Work
Disadvantages of Proof of Work
While Proof of Work (PoW) is one of the most secure and widely used consensus mechanisms, it comes with several drawbacks. Its reliance on high computational power makes it energy-intensive, expensive, and sometimes inefficient for processing transactions quickly. Additionally, PoW networks face issues related to scalability and centralization due to the growing dominance of large mining pools. Below are some of the major disadvantages of PoW:
1. High Energy Consumption
PoW requires miners to perform vast amounts of computational work, consuming large amounts of electricity. Bitcoin alone is estimated to use as much energy as some small countries, raising concerns about its environmental impact.
2. Slow Transaction Speeds and Scalability Issues
PoW networks often struggle with slow transaction processing times. For example, Bitcoin processes around 7 transactions per second, making it inefficient for handling large-scale adoption compared to centralized payment systems like Visa.
3.High Transaction Fees
As network activity increases, transaction fees on PoW blockchains can become expensive. During periods of high congestion, users may have to pay significant fees to get their transactions processed faster.
4. Mining Centralization Risk
Although POW is designed to be decentralized, the high cost of mining hardware and electricity has led to the dominance of large mining pools. This centralization reduces the network’s security and increases the risk of coordinated attacks.
5. 51% Attack Vulnerability
If a single entity or mining pool gains control of more than 51% of a PoW network’s computational power, they could manipulate transactions, reverse payments, and disrupt the blockchain’s integrity. While unlikely for large networks like Bitcoin, smaller PoW networks remain vulnerable.
6. Expensive Hardware Requirements
Mining PoW-based cryptocurrencies requires specialized hardware, such as ASIC (Application-Specific Integrated Circuit) miners, which are expensive and not accessible to everyone. This creates a barrier to entry for individual miners and favors those with significant financial resources.
7. Electronic Waste from Mining Equipment
As mining difficulty increases, older mining hardware becomes obsolete and is discarded. This results in a significant amount of electronic waste, further contributing to environmental concerns.
8. Long Confirmation Times
Due to the time it takes for miners to validate transactions, PoW networks often have long confirmation times. For instance, Bitcoin transactions can take 10 minutes to an hour to be fully confirmed, making them impractical for everyday use.
9. Regulatory and Environmental Scrutiny
Governments and environmental activists are increasingly scrutinizing PoW networks due to their energy consumption. Some countries have even banned or restricted mining operations, which could impact the long-term adoption of PoW-based cryptocurrencies.
10. Not Ideal for Smart Contracts and DeFi Applications
Due to its slow transaction speeds and high costs, PoW is not the best option for smart contracts and decentralized finance (DeFi) applications. This has led to newer blockchain networks adopting alternative consensus mechanisms like Proof of Stake (PoS).
Mining in Proof of Work
Mining is the process that powers the Proof of Work (PoW) consensus mechanism, ensuring the security and integrity of blockchain networks. Miners use specialized hardware to solve complex cryptographic puzzles, competing to add new blocks to the blockchain. This process validates transactions, prevents double-spending, and rewards miners with newly minted cryptocurrency and transaction fees. While mining is essential for maintaining decentralized networks, it requires significant computational power and energy, leading to concerns about scalability and environmental impact. Below are the key aspects of mining in Proof of Work:
Key Aspects of Mining in PoW
- Transaction Validation – Miners verify and group transactions into a block before adding them to the blockchain.
- Cryptographic Puzzle Solving – Miners compete to find a valid hash that meets the network’s difficulty target by adjusting a random value (nonce).
- Mining Rewards – The first miner to solve the puzzle is rewarded with newly minted cryptocurrency (block reward) and transaction fees from the included transactions.
- Mining Hardware – Specialized mining equipment, such as ASIC (Application-Specific Integrated Circuits) and GPUs, are used to increase computational efficiency.
- Mining Difficulty Adjustment – The network automatically adjusts the difficulty level to maintain a consistent block creation time (e.g., Bitcoin’s target is one block every 10 minutes).
- Decentralization and Competition – Mining is an open process where anyone with the necessary hardware can participate, but large mining pools dominate due to high energy and equipment costs.
- 51% Attack Risk – If a single entity controls more than 51% of the network’s mining power, they could manipulate transactions, posing a security risk.
- Energy Consumption – Mining requires substantial electricity, leading to environmental concerns and discussions about sustainable alternatives.
- Mining Pools – Many individual miners join mining pools, where they combine computational power to increase their chances of earning rewards, sharing the profits accordingly.
- Evolution of Mining – As mining becomes more competitive and hardware-intensive, new solutions like renewable energy-powered mining farms and hybrid consensus mechanisms are being explored.
Examples of Cryptocurrencies Using Proof of Work
Proof of Work (PoW) is the original consensus mechanism that powers many of the most well-known cryptocurrencies. It ensures security, decentralization, and transaction validation by requiring miners to solve complex mathematical puzzles. While PoW has faced criticism for its high energy consumption, it remains one of the most trusted methods for securing blockchain networks. Below are some of the most prominent cryptocurrencies that use the Proof of Work mechanism:
Notable Cryptocurrencies Using PoW
- Bitcoin (BTC) – The first and most valuable cryptocurrency, Bitcoin introduced PoW in 2009 and remains the most secure and decentralized network using this mechanism.
- Litecoin (LTC) – Created as a “lighter” version of Bitcoin, Litecoin uses a modified PoW algorithm called Scrypt, allowing for faster block times and lower transaction fees.
- Dogecoin (DOGE) – Initially created as a joke, Dogecoin has gained significant adoption. It shares Litecoin’s Scrypt-based PoW and has a strong community backing.
- Monero (XMR) – A privacy-focused cryptocurrency that uses RandomX, a PoW algorithm designed to be ASIC-resistant, making mining more accessible to individual users.
- Bitcoin Cash (BCH) – A Bitcoin fork that maintains PoW but with larger block sizes to allow faster and cheaper transactions.
- Zcash (ZEC) – A privacy-enhanced cryptocurrency that uses POW along with zk-SNARKs to provide optional anonymous transactions.
- Ethereum Classic (ETC) – A continuation of the original Ethereum blockchain before the DAO hack, still utilizing PoW, unlike Ethereum, which has transitioned to Proof of Stake (PoS).
- Kadena (KDA) – A hybrid PoW blockchain designed for scalability and efficiency, using a unique chain braiding technique to enhance throughput.
- Siacoin (SC) – A decentralized cloud storage network that relies on PoW to secure data transactions.
Comparison of Proof of Work vs. Proof of Stake (PoS)
Proof of Work (PoW) and Proof of Stake (PoS) are two of the most commonly used consensus mechanisms in blockchain technology. Both methods aim to validate transactions and secure decentralized networks, but they operate differently. PoW relies on computational power and mining, while PoS selects validators based on the amount of cryptocurrency they hold and stake in the network. While PoW is known for its high security and decentralization, it requires significant energy consumption, whereas PoS is more energy-efficient and scalable but raises concerns about centralization. Below is a detailed comparison of PoW and PoS.
Comparison Table: PoW vs. PoS
| Feature | Proof of Work (PoW) | Proof of Stake (PoS) |
| Validation Method | Miners solve cryptographic puzzles to validate transactions. | Validators are chosen based on the number of coins staked. |
| Energy Consumption | High; requires extensive computational power. | Low; consumes minimal energy as it doesn’t require mining. |
| Security | Very secure, resistant to attacks due to high computational costs. | Secure but more vulnerable to governance attacks. |
| Transaction Speed | Slower due to mining process (e.g., Bitcoin takes ~10 minutes per block). | Faster as blocks are created without intense computation. |
| Scalability | Limited due to block validation time and energy use. | More scalable with faster transaction processing. |
| Cost to Participate | Requires expensive mining hardware (ASICs, GPUs). | Requires users to stake cryptocurrency; no hardware needed. |
| Centralization Risk | Mining pools can lead to concentration of power. | Wealthier users have more control over validation. |
| 51% Attack Risk | Requires massive computing power to execute. | Possible if an entity holds 51% or more of staked tokens. |
| Environmental Impact | High due to energy consumption. | Low, making it more eco-friendly. |
| Examples of Cryptos Using It | Bitcoin (BTC), Litecoin (LTC), Monero (XMR), Dogecoin (DOGE). | Ethereum (ETH), Cardano (ADA), Solana (SOL), Polkadot (DOT). |
The Future of Proof of Work
The future of Proof of Work (PoW) is at a crossroads as the blockchain industry evolves to address challenges related to scalability, energy consumption, and environmental sustainability. While PoW remains one of the most secure and decentralized consensus mechanisms, its high computational requirements and electricity usage have led to growing concerns. Governments and environmental groups are increasingly scrutinizing PoW-based cryptocurrencies, prompting discussions about more sustainable mining practices, such as using renewable energy sources or developing more energy-efficient hashing algorithms. Additionally, many blockchain networks, including Ethereum, have transitioned from PoW to Proof of Stake (PoS) to improve scalability and reduce environmental impact. However, Bitcoin, the most valuable and widely used cryptocurrency, continues to rely on PoW, and its security and decentralization make it unlikely to shift away from this model anytime soon. Innovations in layer-2 solutions and hybrid consensus mechanisms may help PoW adapt to future demands while retaining its unmatched security. As the blockchain space continues to develop, PoW will likely remain a key player, either in its current form or through refinements that make it more sustainable and efficient.
Conclusion
Proof of Work (PoW) has been the foundation of blockchain security and decentralization since the inception of Bitcoin. While it remains one of the most secure and battle-tested consensus mechanisms, it faces increasing challenges related to energy consumption, scalability, and centralization of mining power. As the blockchain industry evolves, some networks have shifted to alternative consensus mechanisms like Proof of Stake (PoS) to address these limitations. However, PoW continues to offer unmatched security and resistance to attacks, making it a crucial component of the cryptocurrency ecosystem. The future of PoW may involve innovations such as energy-efficient mining practices, hybrid consensus models, and improved scalability solutions. Whether PoW remains dominant or adapts through advancements, its role in securing decentralized networks will continue to shape the evolution of blockchain technology.